Using GitHub actions to monitor Platform.sh deployment status
Take a moment to check out the previous post centered around GitHub actions. It’ll provide a little context, plus go into much more detail about how the status of a Platform.sh deployment can actually be used to trigger workflows on GitHub. Plus, we’re going to build additional jobs in the samepost-deploy.yaml file we started in that post.
Let’s take a look at the file, ignoring the displaylogs job we made previously, and instead focusing on the build
job that sets everything else up:
build):
- Is triggered by all push events that don’t occur on the default branch.
- Places requests on the Status API, until Platform.sh informs GitHub that the environment has either succeeded or failed to deploy the new commits.
- Passes both that final status and the environment’s URL to any subsequent jobs that define
needs.buildin their configuration.
Github actions status checks ensures deployment ease and success
One of the great things about GitHub actions is that I don’t have to write them. If I, for example, wanted to make a quick status check on the environment, I can leverage the generous work of another published action in my workflow pretty easily.test which will:
- Only run if the output of the
buildjob (and the status of my Platform.sh environment) is successful. - Will
usethelakuapi/gh-actions-http-statuspublic action to place a request on the environment URL also retrieved from thebuildjob. - Apply an expected status to that request. If the statuses match, the step will pass, adding another check to my pull request. Should it receive a 404 or 503, the step fails and we can go investigate where the deployment fell short.
sites array, with matching expected statuses that will show up as separate steps in my final workflow for the push.
Configuring Lighthouse with GitHub actions to monitor user experience
Status checks for GitHub actions are great, but what I really want to know is whether a pull request is modifying the experience a user has when they visit my application in some negative way. Once again, I can add a job that uses a publicly available GitHub action - in this case, to perform a Lighthouse audit on my environment URL. To start, we can add a few workflow-level environment variables topost-deploy.yaml
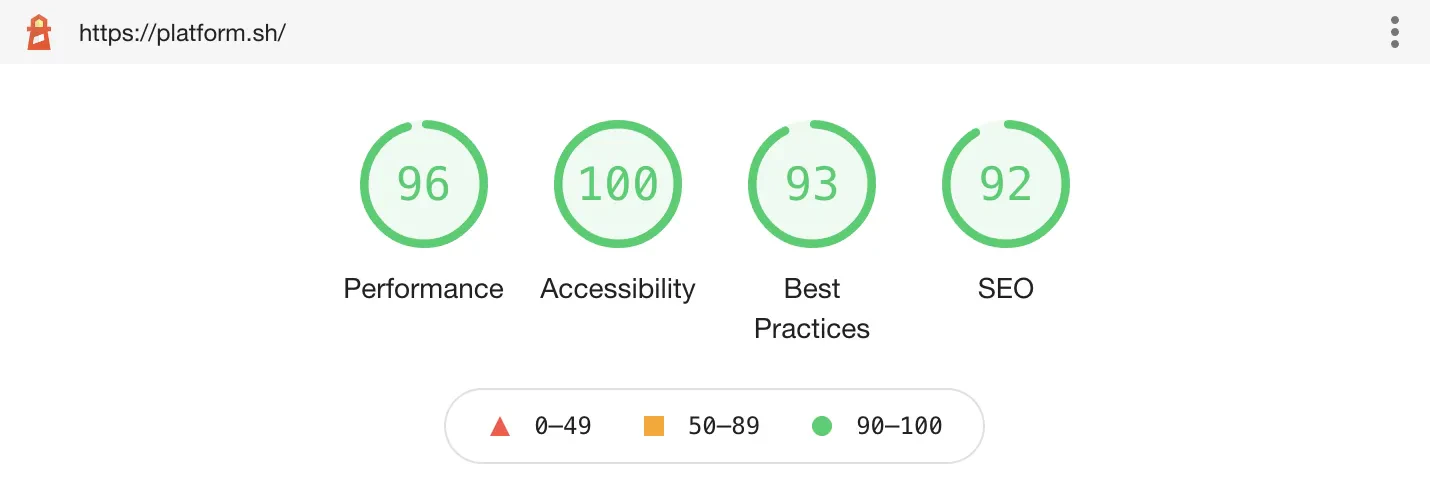
audit which uses the
jakejarvis/lighthouse-action GitHub action, first focusing
on the Accessibility audit.
audit job will:
- Only run on pushes to a branch associated with a pull request integrated with a Platform.sh environment that has
successfully deployed. (See
buildabove) - Use the
jakejarvis/lighthouse-actionaction with the environment URL passed along from thebuildjob. - Upload the full report as a workflow artifact, so that we can inspect individual recommendations in detail later.
- The action will also save a local copy of the report in two formats - html and JSON - in a
reportsubdirectory. We can then use thejqtool to retrieve the accessibility score. - Run a simple test based on the Accessibility audit using the
ACC_MINthreshold we set previously. In this case, if the accessibility score for our environment is below 90%, the step and workflow will fail for the push.